Search engines play a significant role in extracting critical details about a
target from the Internet. Several search engines have the ability to focus on
organisational data, including technology systems, personnel profiles, login
pages, intranet portals, contact information, and so forth. The report helps
the attacker perform social engineering and other advanced system
attacks.
Let's first examine the inner workings of search engines. Crawlers, a type of
automated software used by search engines, are used to continuously scan live
websites and add the results to the search engine index, which is then saved
in a vast database. A list of Search Engine Results Pages (SERPs) is returned
when a user queries the search engine index. These outcomes include web pages,
videos, photos, and numerous more file types sorted and presented based on
relevancy.
Examples of major search engines include Google, DuckDuckGo, Bing, Yahoo, Ask,
Baidu, WolframAplha, and StartPage. Attackers can find, filter, and sort
specific information on the target using advanced search operators offered by
these search engines and creating complex searches. One of the example of
queries is Google Dorks.
There are various ways and techniques to gather information using search
engines, from which a few are mentioned below:
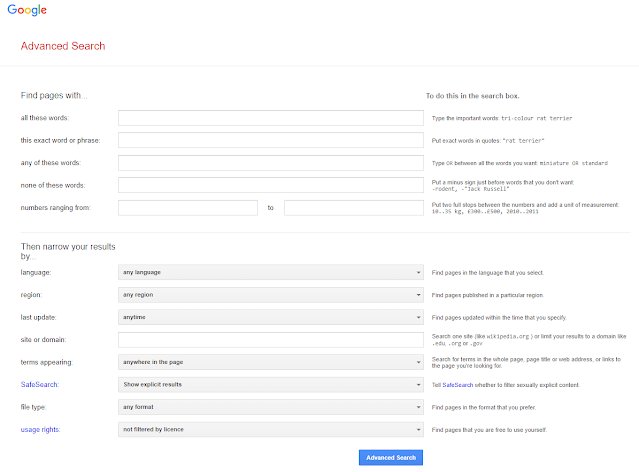
One can conduct a more thorough, sophisticated and accurate web search
with the help of Google Advanced Search and Advanced Image Search. Without
having to type or remember the sophisticated operators (Google Dorks), you
can utilise these search features to obtain the same level of
precision.
Google Advance Search
To carry out an Advance Google search,
Google Advance Image Search
You can use an image as a search query with reverse image search. The search
engine verifies the search engine index and displays all the online
locations of the image on the search results page. The outcomes can assist
you in tracing the origin and specifics of images, including photos, profile
pictures, and memes. Attackers can use tools like,
Internet-based search engines called "video search engines" search the web
for video information. Since it may be utilised to learn more about the
target, video content found using video search engines has significant
value. Engines like
YouTube,
Google Videos, Yahoo Videos, and
Bing Videos can help an attacker search for video-based
content.
After examining the video, an attacker can continue to examine the
video's content to discover secret data like the time/date and the
video's thumbnail. An attacker can transform a video into text and
other formats and extract crucial information about the target by using
video analysis programmes like YouTube DataViewer, EXGif,
and VideoReverser.com.
Meta search engines are a different kind of search engine. To get their own
results, these search engines send their queries to other search engines
(such as Google, Bing, Ask.com, etc.). Additionally, meta-search engines
have a feature that filters away duplicate search results so that they won't
be shown twice if a user does the same search query again.
Attackers can obtain a great deal of detailed information by querying many
search engines using meta-search engines like
Startpage, MetGer, and eTools.ch. By masking the user's IP
address, meta-search engines also give search engine users anonymity.
An attacker can take control of CCTV cameras, traffic control systems,
Internet-connected home appliances, Supervisory Control and Data Acquisition
(SCADA) systems, industrial equipment, etc. by conducting a simple search on
IoT search engines. IoT search engines like Censys, Shodan, and
Thingful make it easier for attackers to get target information. Many
of them either use default credentials that are easily exploitable or
operate without passwords. The attacker can access such IoT devices and
carry out additional assaults using information like the IP address,
location, hostname, and open ports.
FTP servers are widely used by businesses, industries, and academic
institutions to store massive file archives and other software that are
shared among their staff members. Numerous servers are accessible directly
through web browsers and are unprotected. Attackers can look for crucial
files and directories with important data using FTP search engines such as
NAPALM FTP Indexer, Global FTP Search Engine, and
FreewareWeb FTP File Search.
As an ethical hacker, you can ask the search
engine to delete any removed pages or information about your business that you
discover in SERPs or the search engine cache.
You might be also interested in,
We hope this helps. If any suggestions or doubts you can add a comment and we
will reply as soon as possible.



%20Cover.jpg)
%20Cover.jpg)



No comments:
Post a Comment